Authoeiryt Error Please Try Again With Correct Id
This browser is no longer supported.
Upgrade to Microsoft Edge to take reward of the latest features, security updates, and technical back up.
Troubleshoot Azure Active Directory Pass-through Authentication
This article helps you find troubleshooting information about common issues regarding Azure Advertisement Pass-through Hallmark.
Of import
If yous are facing user sign-in bug with Pass-through Authentication, don't disable the characteristic or uninstall Pass-through Authentication Agents without having a cloud-but Global Ambassador business relationship or a Hybrid Identity Administrator account to fall back on. Larn most adding a deject-only Global Ambassador business relationship. Doing this stride is critical and ensures that y'all don't get locked out of your tenant.
General issues
Cheque status of the characteristic and Authentication Agents
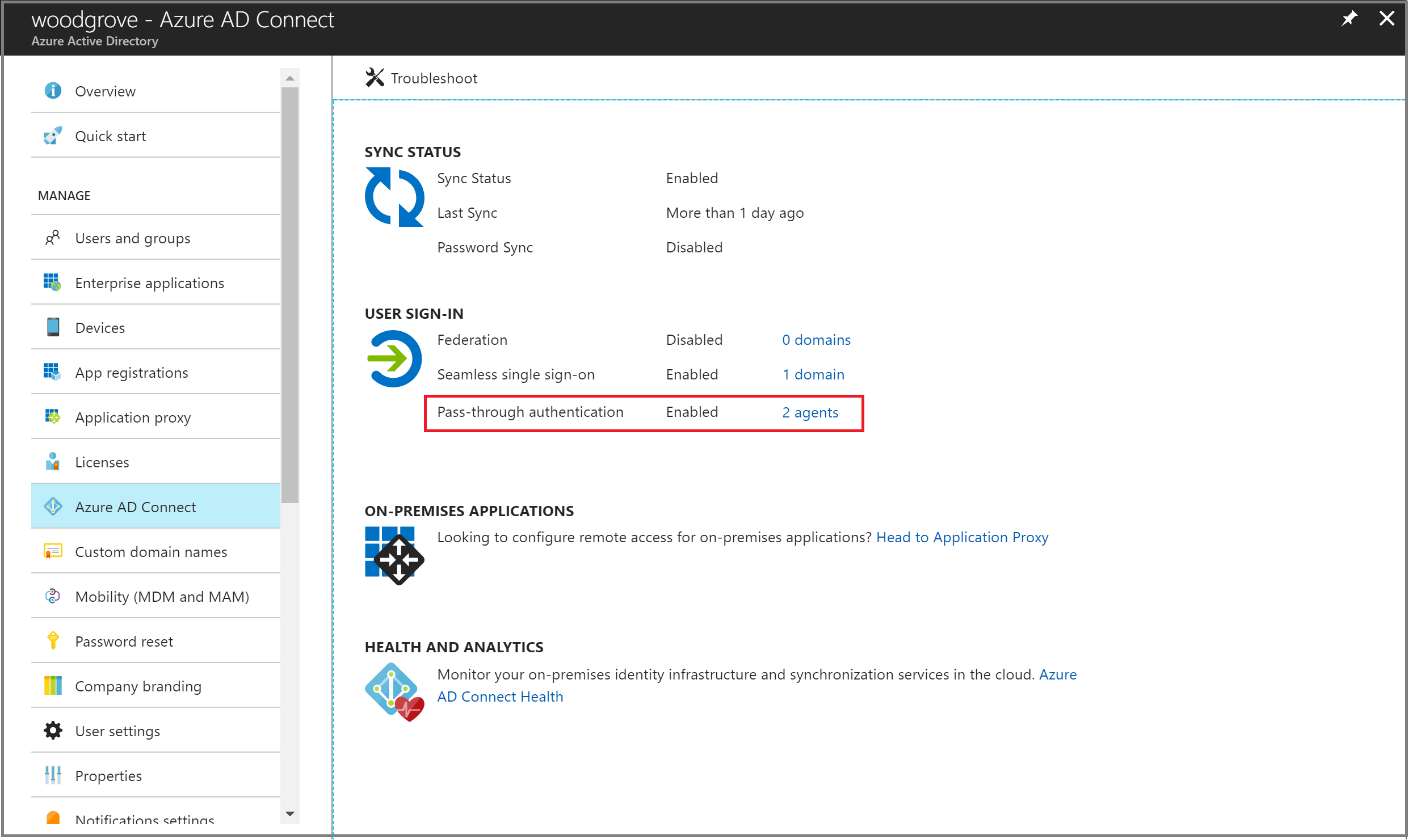
Ensure that the Pass-through Authentication feature is even so Enabled on your tenant and the condition of Authentication Agents shows Active, and not Inactive. Y'all tin check status by going to the Azure AD Connect bract on the Azure Agile Directory admin center.

User-facing sign-in fault messages
If the user is unable to sign into using Pass-through Authentication, they may see 1 of the following user-facing errors on the Azure Advert sign-in screen:
| Fault | Description | Resolution |
|---|---|---|
| AADSTS80001 | Unable to connect to Active Directory | Ensure that agent servers are members of the same AD forest every bit the users whose passwords need to exist validated and they are able to connect to Active Directory. |
| AADSTS8002 | A timeout occurred connecting to Active Directory | Check to ensure that Agile Directory is available and is responding to requests from the agents. |
| AADSTS80004 | The username passed to the agent was not valid | Ensure the user is attempting to sign in with the right username. |
| AADSTS80005 | Validation encountered unpredictable WebException | A transient mistake. Retry the request. If it continues to fail, contact Microsoft support. |
| AADSTS80007 | An error occurred communicating with Active Directory | Check the amanuensis logs for more information and verify that Agile Directory is operating every bit expected. |
Users go invalid username/password mistake
This tin happen when a user's on-bounds UserPrincipalName (UPN) is different than the user'southward cloud UPN.
To confirm that this is the issue, outset test that the Pass-through Authentication agent is working correctly:
-
Create a test account.
-
Import the PowerShell module on the agent machine:
Import-Module "C:\Plan Files\Microsoft Azure AD Connect Authentication Agent\Modules\PassthroughAuthPSModule\PassthroughAuthPSModule.psd1" -
Run the Invoke PowerShell command:
Invoke-PassthroughAuthOnPremLogonTroubleshooter -
When y'all are prompted to enter credentials, enter the same username and password that are used to sign in to (https://login.microsoftonline.com).
If you get the same username/password error, this means that the Pass-through Authentication amanuensis is working correctly and the issue may be that the on-premises UPN is non-routable. To larn more, encounter Configuring Alternate Login ID.
Important
If the Azure Advert Connect server isn't domain joined, a requirement mentioned in Azure AD Connect: Prerequisites, the invalid username/password issue occurs.
Sign-in failure reasons on the Azure Agile Directory admin center (needs Premium license)
If your tenant has an Azure Advertizement Premium license associated with information technology, you can also look at the sign-in activity written report on the Azure Agile Directory admin center.

Navigate to Azure Agile Directory -> Sign-ins on the Azure Active Directory admin center and click a specific user's sign-in activity. Look for the SIGN-IN Mistake CODE field. Map the value of that field to a failure reason and resolution using the following tabular array:
| Sign-in fault code | Sign-in failure reason | Resolution |
|---|---|---|
| 50144 | User'due south Active Directory password has expired. | Reset the user's countersign in your on-premises Agile Directory. |
| 80001 | No Hallmark Agent bachelor. | Install and annals an Authentication Amanuensis. |
| 80002 | Authentication Agent'due south password validation asking timed out. | Bank check if your Active Directory is reachable from the Authentication Agent. |
| 80003 | Invalid response received past Authentication Amanuensis. | If the problem is consistently reproducible across multiple users, cheque your Agile Directory configuration. |
| 80004 | Incorrect User Principal Name (UPN) used in sign-in asking. | Enquire the user to sign in with the correct username. |
| 80005 | Authentication Agent: Error occurred. | Transient fault. Endeavor once more later. |
| 80007 | Authentication Agent unable to connect to Active Directory. | Check if your Active Directory is reachable from the Authentication Agent. |
| 80010 | Hallmark Agent unable to decrypt password. | If the trouble is consistently reproducible, install and register a new Hallmark Agent. And uninstall the current ane. |
| 80011 | Authentication Amanuensis unable to call back decryption key. | If the problem is consistently reproducible, install and register a new Authentication Agent. And uninstall the current 1. |
| 80014 | Validation asking responded after maximum elapsed time exceeded. | Authentication agent timed out. Open a back up ticket with the error lawmaking, correlation ID, and timestamp to get more details on this error |
Important
Pass-through Authentication Agents authenticate Azure AD users by validating their usernames and passwords confronting Active Directory past calling the Win32 LogonUser API. Equally a upshot, if you have set the "Logon To" setting in Active Directory to limit workstation logon admission, you will have to add servers hosting Pass-through Authentication Agents to the list of "Logon To" servers likewise. Failing to do this volition block your users from signing into Azure Advertizement.
Authentication Agent installation issues
An unexpected error occurred
Collect agent logs from the server and contact Microsoft Support with your issue.
Authentication Amanuensis registration issues
Registration of the Hallmark Amanuensis failed due to blocked ports
Ensure that the server on which the Authentication Amanuensis has been installed tin can communicate with our service URLs and ports listed hither.
Registration of the Hallmark Agent failed due to token or account dominance errors
Ensure that you use a cloud-just Global Administrator account or a Hybrid Identity Administrator account for all Azure AD Connect or standalone Authentication Agent installation and registration operations. There is a known consequence with MFA-enabled Global Administrator accounts; plough off MFA temporarily (only to complete the operations) as a workaround.
An unexpected error occurred
Collect agent logs from the server and contact Microsoft Support with your event.
Hallmark Agent uninstallation issues
Alarm message when uninstalling Azure Advertisement Connect
If you lot have Pass-through Authentication enabled on your tenant and you try to uninstall Azure Advertizing Connect, it shows y'all the following alarm bulletin: "Users will not exist able to sign-in to Azure Advert unless you have other Pass-through Authentication agents installed on other servers."
Ensure that your setup is highly available earlier you uninstall Azure AD Connect to avoid breaking user sign-in.
Issues with enabling the characteristic
Enabling the feature failed considering there were no Hallmark Agents available
You need to have at least one agile Authentication Agent to enable Pass-through Hallmark on your tenant. You tin can install an Authentication Agent by either installing Azure AD Connect or a standalone Authentication Agent.
Enabling the feature failed due to blocked ports
Ensure that the server on which Azure Ad Connect is installed can communicate with our service URLs and ports listed here.
Enabling the characteristic failed due to token or account authorization errors
Ensure that you use a cloud-only Global Administrator business relationship when enabling the feature. At that place is a known issue with multi-factor hallmark (MFA)-enabled Global Administrator accounts; turn off MFA temporarily (only to consummate the operation) every bit a workaround.
Collecting Pass-through Hallmark Agent logs
Depending on the type of event you may have, yous need to look in different places for Pass-through Hallmark Amanuensis logs.
Azure AD Connect logs
For errors related to installation, check the Azure Advertizing Connect logs at %ProgramData%\AADConnect\trace-*.log.
Authentication Agent event logs
For errors related to the Authentication Agent, open upwardly the Event Viewer application on the server and check under Application and Service Logs\Microsoft\AzureAdConnect\AuthenticationAgent\Admin.
For detailed analytics, enable the "Session" log (right-click inside the Effect Viewer awarding to detect this option). Don't run the Authentication Amanuensis with this log enabled during normal operations; employ only for troubleshooting. The log contents are just visible after the log is disabled again.
Detailed trace logs
To troubleshoot user sign-in failures, expect for trace logs at %ProgramData%\Microsoft\Azure AD Connect Authentication Agent\Trace\. These logs include reasons why a specific user sign-in failed using the Pass-through Authentication feature. These errors are also mapped to the sign-in failure reasons shown in the preceding sign-in failure reasons tabular array. Following is an example log entry:
AzureADConnectAuthenticationAgentService.exe Error: 0 : Passthrough Authentication request failed. RequestId: 'df63f4a4-68b9-44ae-8d81-6ad2d844d84e'. Reason: '1328'. ThreadId=v DateTime=xxxx-xx-xxTxx:twenty:xx.xxxxxxZ You tin get descriptive details of the fault ('1328' in the preceding example) by opening upwards the command prompt and running the post-obit command (Note: Replace '1328' with the actual error number that you see in your logs):
Internet helpmsg 1328

Domain Controller logs
If audit logging is enabled, additional data tin exist found in the security logs of your Domain Controllers. A unproblematic mode to query sign-in requests sent by Pass-through Authentication Agents is as follows:
<QueryList> <Query Id="0" Path="Security"> <Select Path="Security">*[EventData[Data[@Name='ProcessName'] and (Data='C:\Plan Files\Microsoft Azure Advertisement Connect Authentication Amanuensis\AzureADConnectAuthenticationAgentService.exe')]]</Select> </Query> </QueryList> Functioning Monitor counters
Another way to monitor Authentication Agents is to rails specific Operation Monitor counters on each server where the Authentication Agent is installed. Use the following Global counters (# PTA authentications, #PTA failed authentications and #PTA successful authentications) and Mistake counters (# PTA authentication errors):

Important
Pass-through Authentication provides high availability using multiple Authentication Agents, and not load balancing. Depending on your configuration, not all your Hallmark Agents receive roughly equal number of requests. It is possible that a specific Authentication Agent receives no traffic at all.
Feedback
Submit and view feedback for
Source: https://docs.microsoft.com/en-us/azure/active-directory/hybrid/tshoot-connect-pass-through-authentication
0 Response to "Authoeiryt Error Please Try Again With Correct Id"
Enviar um comentário